Online research and assignment writing have become integral parts of our lives, whether you’re a student, a professional, or simply an individual seeking information in the digital age. The world’s vast repository of knowledge is at our fingertips, accessible with just a few clicks. However, with this unprecedented access to information comes an equally unprecedented need for security. When implementing best practices for online research and assignment writing security, consider using resources like LiaHelp for your assignments to further enhance your academic integrity and data protection.
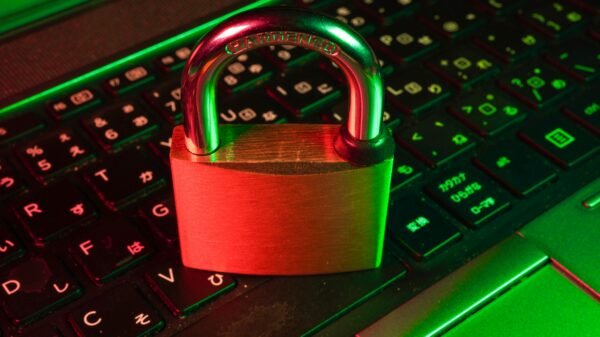
In the digital age, security has taken on an unparalleled significance. The internet has transformed the way we conduct research and craft assignments, opening up new avenues for learning and information sharing. However, it has also exposed us to a multitude of security threats. From data breaches that can compromise sensitive information to plagiarism concerns that undermine the integrity of your work, and even the ever-present menace of malware and phishing attacks, there are numerous perils that we must navigate in this virtual realm.
The Risks
One of the most pressing concerns in the digital age is the risk of data breaches. These breaches can occur in various forms, from unauthorized access to personal information stored online to the inadvertent sharing of sensitive data. They have the potential to expose your personal details, research data, and assignment content to malicious individuals or organizations. Understanding how data breaches happen and taking steps to prevent them is paramount.
Plagiarism is a pervasive issue in academic and professional settings. It involves the unauthorized use of someone else’s work, ideas, or intellectual property without proper attribution. In online research and assignment writing, plagiarism can undermine the originality and credibility of your work, potentially leading to academic or professional repercussions. It’s vital to be aware of what constitutes plagiarism and how to avoid it.
Malware, short for malicious software, and phishing attacks are tactics employed by cybercriminals to compromise your digital security. Malware can infiltrate your devices and steal your data, while phishing attacks are cleverly disguised attempts to trick you into revealing sensitive information. Recognizing the signs of these attacks and learning how to protect yourself against them is essential in the digital age.
Inadequate security measures can have far-reaching consequences. A data breach can lead to identity theft or financial loss, while plagiarism can damage your reputation and result in severe academic or professional penalties. Malware and phishing attacks can disrupt your work, compromise your data, and lead to significant inconvenience and stress. The stakes are high when it comes to online research and assignment writing, making it imperative to prioritize security in these endeavors.
Best Practices for Online Research Security
In online research, safeguarding your personal information is a foundational step in ensuring your digital security. Strong, unique passwords serve as the first line of defense against unauthorized access to your accounts and research data. They should be a combination of letters, numbers, and special characters, and it’s crucial to avoid easily guessable information like birthdays or common words. Regularly updating your passwords and refraining from using the same password across multiple platforms further bolsters your protection.
Ensuring the highest level of security and authenticity in your online research and assignment writing practices goes hand in hand with seeking trustworthy services to write my paper. In addition to robust passwords, two-factor authentication (2FA) provides an extra layer of security. This authentication method necessitates not only your password but also a secondary code that is typically sent to your mobile device. 2FA adds an additional hurdle for potential attackers, making it significantly more challenging for them to gain access to your research-related accounts.
The security of your online research efforts is intricately tied to the nature of your internet connection. Using a Virtual Private Network (VPN) can be an invaluable tool for maintaining privacy and security while conducting research. A VPN encrypts your internet traffic and hides your IP address, ensuring that your online activities remain confidential and less susceptible to eavesdropping or surveillance.
Equally important is the practice of avoiding public Wi-Fi networks for sensitive tasks. Public Wi-Fi, while convenient, is often unsecured and poses a substantial risk. Attackers can intercept data on open networks, potentially compromising your research or assignments. Whenever possible, opt for trusted and encrypted Wi-Fi networks, or rely on your mobile data connection to maintain a higher level of security.
Evaluating the credibility of your research sources is an essential aspect of ensuring the quality and integrity of your work. In the age of information overload, misinformation, and biased reporting, this practice is more critical than ever. When conducting online research, take time to assess the credibility of websites and sources you encounter. Look for clear authorship, publication dates, and citations to reliable references within the content. Peer-reviewed journals, academic institutions, and well-established organizations often provide trustworthy sources for your research.
Beyond assessing credibility, recognizing bias and misinformation is equally important. Critical thinking is your ally here, as it allows you to discern potential biases and inaccuracies in the information you encounter. Cross-reference data and compare findings from multiple sources to ensure a well-rounded and reliable foundation for your research. Remember that misinformation can sometimes be subtle, making the ability to critically evaluate sources an invaluable skill in the digital age. By integrating these practices into your online research routine, you can significantly enhance the security and integrity of your work.
Best Practices for Assignment Writing Security
Assignment writing security is a paramount concern, especially in educational and professional settings where originality, accuracy, and data integrity are of utmost importance. Here, we explore best practices to safeguard your assignment writing endeavors.
Preventing plagiarism is a fundamental aspect of maintaining the integrity of your assignments. When drawing from external sources, be it research papers, articles, or other works, it’s essential to properly cite and reference the original authors. This not only acknowledges their work but also establishes the credibility and authenticity of your own assignment. Familiarize yourself with the citation style recommended by your institution or publisher, whether it’s APA, MLA, Chicago, or another format, and apply it consistently throughout your work.
In addition to manual citation and referencing, consider employing plagiarism detection tools to check your work for unintentional similarities with existing content. These tools compare your assignment against a vast database of texts and highlight any potentially problematic matches. They serve as a valuable safety net, helping you identify and rectify any accidental instances of plagiarism before submitting your work.
Effective document management and version control are critical for assignment writing security, ensuring that your work is protected from data loss, corruption, or unauthorized access.
Storing your assignment documents in the cloud offers multiple benefits, including data redundancy and accessibility from anywhere. Services like Google Drive, Dropbox, or OneDrive automatically back up your files and provide version history, allowing you to recover previous iterations of your work in case of errors or data loss. Cloud storage also minimizes the risk of losing your entire assignment due to a device failure.
In addition to cloud storage, it’s prudent to maintain a version control system for your assignments. This involves saving multiple versions of your work, each time you make significant edits or updates. Renaming files with version numbers or dates can help you keep track of changes and revert to a previous version if necessary. Such practices are especially valuable when working collaboratively, as they offer a secure method to manage and track alterations made by multiple contributors.
Collaboration is common in academic and professional assignments, but it comes with its own security considerations.
Utilizing secure and reputable collaboration platforms, such as Google Workspace or Microsoft Teams, helps ensure the privacy and integrity of your assignment during the collaborative writing process. These platforms often provide features like access controls, document permissions, and encryption, which help protect your work from unauthorized access or tampering.
When collaborating on assignments, it’s crucial to control access and permissions carefully. Only grant access to those individuals who genuinely need it and assign appropriate roles and permissions based on their level of involvement. This minimizes the risk of data breaches and ensures that your assignment remains under your control. Additionally, always follow institution or organization-specific guidelines for sharing and collaborating on sensitive documents.
By adhering to these best practices for assignment writing security, you can maintain the integrity and privacy of your work while collaborating effectively with others. These measures not only protect your content but also ensure that your assignments are a true reflection of your knowledge and effort.
Also Read:
How To Unblock And Play Unblocked Games 66EZ – 4 Alternatives
Enhance Your Trading Decision-Making With GOC Technology’s Next-Gen FinTech Solutions