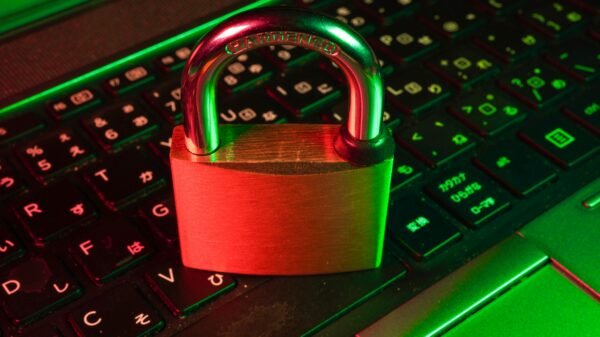
Network security for business stands as one of the most critical components. It forms a bastion against the ceaseless tide of cyber threats. This grows in sophistication with every heartbeat of digital innovation.
But to stand guard is not enough. IT network security management must follow the latest trends to fortify their defenses.
This expansive exploration will unfurl the latest strategies and technologies. Armoring the modern IT network. Organizations can better protect their data, assets, and reputation.
Read on to learn more.
The Role of AI and Machine Learning in Network Security
Artificial Intelligence (AI) and Machine Learning (ML) have emerged as more than buzzwords. They are now severe allies in the war against cybercrime.
These technologies excel at preempting threats. This is by analyzing patterns and anomalies faster and more than any human.
Security teams can automate the detection of:
- potential breaches
- correlate vast amounts of data for robust threat intelligence
- even predict future attack vectors
Predictive Analytics
Predictive analytics is a subset of AI that focuses on anticipating future outcomes. This is based on historical data and analytics techniques such as ML.
Predictive analytics can forecast potential security incidents. Providing IT managers with the foresight to reinforce their defenses.
Threat Detection and Response
AI-powered systems can check IT networks for suspicious activity. When a potential threat is identified, automated responses can be initiated, such as:
- isolating infected devices
- quarantining malware
- alerting IT staff for further investigation
Zero Trust Architecture: The New Paradigm
Conventional security models operate on trust but verification. It challenges this notion and operates on never trusting, consistently verifying.
ZTA divides networks into smaller segments and secures them. Requiring strict verification for any attempted connection. This enhances security and protects against lateral movement by attackers.
Micro-Segmentation
Micro-segmentation is a core tenet of ZTA. Dividing the network into tiny segments, each with its security standards. This strategy minimizes the impact of breaches and contains threats.
Continuous Authentication
With ZTA, traditional network perimeters dissolve. Continuous authentication comes into play.
Ensuring that every user or device that accesses the network is verified. It also minimizes the window of opportunity for attackers.
Blockchain for Enhanced Security and Transparency
The inherent security features are causing ripples in management network security. This is by providing a tamper-proof, decentralized ledger of transactions and blockchain.
This can record and establish the following:
- provenance of data
- detect unauthorized changes
- increase transparency
Data Integrity
The integrity of data is a significant concern in cyber security. Blockchain’s immutable nature ensures that once data is added to the chain.
It cannot be altered without the consensus of the network participants. It provides a robust mechanism for maintaining data integrity.
Decentralization
Blockchain mitigates the risk of a single point of failure. Decentralization can prevent large-scale attacks by distributing the control of the network.
Network Access Control (NAC) – The Gatekeeper
Network Access Control (NAC) is an approach to computer security. It attempts to unify endpoint security technology such as:
- antivirus
- host intrusion prevention
- vulnerability assessment
NAC ensures that only the right people with the proper access connect to the network.
Real-time Visibility
NAC solutions provide real-time visibility into every device. This enables IT security managers to oversee who and what is trying to gain access.
Policy Enforcement at the Edge
NAC can enforce security policies at the network perimeter before allowing entry. It establishes a baseline for regular network activity. Deviations from this baseline trigger an alert or block access.
Cloud Native Security: Protecting Digital Transformation
The proliferation of cloud services has prompted the need for security solutions. It addresses the unique security challenges presented by cloud-based systems, such as:
- multi-tenancy
- shared responsibility models
- distributed nature of cloud infrastructure
Automated Security in Pipeline
Cloud Native Security involves the integration of security into the DevOps pipeline. Adhering to the principle of “Security as Code.”
You must automate security checks at the earliest phases of development. This can identify and rectify vulnerabilities before deployment, reducing the attack surface.
Container Security
Containers offer a lightweight, efficient means of packaging applications. Cloud Native Security focuses on securing these containers from the build process. This is to deployment and beyond, ensuring that only safe runs in production.
Enhanced Identity and Access Management (IAM)
Identity and Access Management (IAM) system is the linchpin of adequate network security. Securing every digital identity and managing their access privileges has become complex.
Multi-Factor Authentication (MFA)
MFA is a method of confirming a user’s claimed identity. This is by combining two different components. IAM systems that incorporate MFA add a valuable layer of security.
Users must provide methods of identification:
- something they know (a password)
- something they have (a security token)
- something they are (a biometric feature)
Role-Based Access Control (RBAC)
RBAC is a method of restricting network access based on a user’s role within an organization. IAM systems that use RBAC can streamline access management.
Ensuring that users only have the permissions necessary to fulfill their role. Reducing the risk of data breaches due to over-entitled users.
The Rise of Quantum Computing in Network Security
Quantum computing presents both an opportunity and a challenge for network security. The immense computing power of quantum systems can break through conventional encryption methodologies. This same power can be harnessed to develop new cryptographic techniques.
Post-Quantum Cryptography
Post-quantum cryptography is gaining momentum. This involves developing encryption methods that can withstand the brute-force solving capabilities.
Quantum Key Distribution (QKD)
Quantum Key Distribution represents a revolutionary approach to secure communications. Utilizing the principles of quantum mechanics to generate and share encryption keys. What sets QKD apart is its ability to detect any attempt at interception.
Understanding the Latest Trends in IT Network Security Management
IT network security management is akin to opening the gates to digital calamity. Incorporating the latest trends can help security managers keep their systems safe. Organizations must stay vigilant, for the digital horizon is shifting.
Adopting ZTA for a more secure architecture. This can craft a robust, multi-layered defense that adapts to adversaries. An informed approach to network security is no longer a competitive advantage.
For more helpful tips, check out the rest of our site today!